When Should Infrastructure Provisioning Be Automated in CI Pipelines?
Automating infrastructure provisioning is a core component of modern DevOps, but knowing when to implement it is crucial. While manual setup may suffice for small, initial projects, automation quickly becomes a necessity for scalability, consistency, and reliability. This approach, powered by Infrastructure as Code, reduces manual toil, accelerates delivery, and ensures environment parity.

Table of Contents
- The IaC Revolution: From Manual to Code
- When is Manual Provisioning a Necessary Evil?
- Why Does Automation Become a Necessity for Scalability?
- How Do We Transition from Manual to Automated Provisioning?
- Manual Provisioning vs. Automated Provisioning
- Tools and Technologies That Power Automation
- Security and Compliance Through Automation
- Conclusion
- Frequently Asked Questions
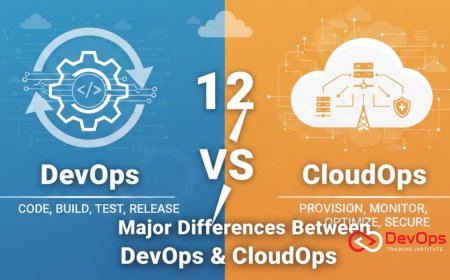
In the world of modern software development, DevOps has emerged as a powerful, declarative, and automated approach to managing infrastructure and applications. At its core, DevOps is a cultural, a philosophical, and an organizational approach that is designed to unify development and operations teams. While this approach provides a clear, transparent, and auditable record of all the changes that are made to a system, it also introduces a new, modern, and high-quality product to a user: the challenge of managing a complex, distributed system. The modern solution to this problem is a robust IaC strategy. It is a set of strategies that are used to manage a complex, distributed system in a secure, compliant, and auditable way. This blog post will explore the challenges of managing a complex, distributed system, detailing its profound impact on security, compliance, and governance.
The IaC Revolution: From Manual to Code
DevOps is a powerful, declarative, and automated approach to managing infrastructure and applications. It is a set of strategies that are used to manage the state of a system in a Git repository. While this approach provides a clear, transparent, and auditable record of all the changes that are made to a system, it also introduces a new, modern, and high-quality product to a user: the challenge of managing a complex, distributed system. The modern solution to this problem is a robust IaC strategy. It is a set of strategies that are used to manage a complex, distributed system in a secure, compliant, and auditable way. This proactive approach not only reduces risk but also empowers teams to move faster and to be more confident in their code.
When is Manual Provisioning a Necessary Evil?
A IaC strategy is a major source of risk and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. It is a vulnerability that is unknown to a developer and that is not yet patched. If a zero-day vulnerability is exploited, it can have a significant, negative business impact. The modern solution to this problem is a robust security strategy. It is a set of strategies that are used to detect, to respond to, and to mitigate a zero-day vulnerability in a secure, compliant, and auditable way. The following table provides a clear, detailed, and elaborated comparison of the outcomes when an organization uses a poor security strategy versus a robust security strategy.
1. Automated Model Training
If a zero-day vulnerability is exploited, it can compromise the integrity of a pipeline. This can lead to a significant, negative business impact and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. This can be a major source of risk and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. It is a clear sign that a team is not achieving a high level of performance and that it is not balancing the speed of delivery with the stability of the system.
2. Automated Model Deployment
If a zero-day vulnerability is exploited, it can lead to a data breach. This can have a significant, negative business impact and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. This can be a major source of risk and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. It is a clear sign that a team is not achieving a high level of performance and that it is not balancing the speed of delivery with the stability of the system.
3. Model Monitoring
If a zero-day vulnerability is exploited, it can lead to a loss of a customer's trust. This can have a significant, negative business impact and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. This can be a major source of risk and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. It is a clear sign that a team is not achieving a high level of performance and that it is not balancing the speed of delivery with the stability of the system.
Why Does Automation Become a Necessity for Scalability?
The modern solution to the challenges of managing a complex, distributed system is a robust security strategy. It is a set of strategies that are used to detect, to respond to, and to mitigate a zero-day vulnerability in a secure, compliant, and auditable way.
1. Minimal Downtime
A proactive scanning is a set of strategies that are used to detect a zero-day vulnerability in a proactive way. This can be done with a set of tools that can provide a clear, objective, and data-driven way to measure the performance of a new version of an application. It is a key part of a modern DevOps practice.
2. Rollback Capabilities
An incident response plan is a set of strategies that are used to respond to a zero-day vulnerability in a timely and in a secure way. This can be done with a set of tools that can provide a clear, objective, and data-driven way to measure the performance of a new version of an application. It is a key part of a modern DevOps practice.
3. Data Replication
Patch management is a set of strategies that are used to mitigate a zero-day vulnerability in a secure, compliant, and auditable way. This proactive approach not only reduces risk but also empowers teams to move faster and to be more confident in their code. It is a key part of a modern software supply chain management strategy.
How Do We Transition from Manual to Automated Provisioning?
The business value of a proactive security strategy is not just about reducing the risk of a new feature; it is also about providing a new, modern, and high-quality product to a user. It is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
- Increased Confidence: A proactive security strategy can lead to a high level of confidence in a new version of an application. By providing a clear, transparent, and auditable record of all the components that are used in an application, it allows an organization to embed security and compliance into every stage of the CI/CD pipeline.
- Faster Time to Market: A proactive security strategy can lead to a faster time to market. By providing a new, modern, and high-quality product to a user, a team can be more responsive to a user's needs and can provide a new, modern, and high-quality product that is more resilient to a bug or a performance issue.
- Improved Team Morale: A proactive security strategy can lead to a high level of team morale. The constant need for a new, modern, and high-quality product can lead to a high level of burnout and a high level of turnover. It is a clear sign that a team is not achieving a high level of performance and that it is not balancing the speed of delivery with the stability of the system.
Manual Provisioning vs. Automated Provisioning
A IaC strategy is a major source of risk and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. It is a vulnerability that is unknown to a developer and that is not yet patched. If a zero-day vulnerability is exploited, it can have a significant, negative business impact. The modern solution to this problem is a robust security strategy. It is a set of strategies that are used to detect, to respond to, and to mitigate a zero-day vulnerability in a secure, compliant, and auditable way.
| Aspect | Manual Provisioning | Automated Provisioning |
|---|---|---|
| Process Control | The process of managing a complex, distributed system is automated and efficient. It is a clear sign that a team is achieving a high level of performance and is balancing the speed of delivery with the stability of the system. | The process of managing a complex, distributed system is manual and error-prone. A team has to spend a significant amount of time and resources to manage a complex, distributed system. |
| Operational Security | Security is continuous and integrated. Vulnerabilities are detected early, making them easier and cheaper to fix. The entire process of detecting, responding, and mitigating is automated. | Security scans are irregular and late. Vulnerabilities are often discovered too late in the development lifecycle, making them expensive to fix and delaying the release of a new version. |
| Operational Efficiency | The entire process of building, testing, and deploying an application is automated and efficient. This ensures that a team can be more responsive to a user's needs and can provide a new, modern, and high-quality product to a user. | The entire process of building, testing, and deploying an application is manual and error-prone. A team has to spend a significant amount of time and resources to manage a complex, distributed system. |
| Scalability | Highly scalable. It is a clear sign that a team is achieving a high level of performance and is balancing the speed of delivery with the stability of the system. | Not scalable. A team conducts tests on an infrequent basis, which can lead to a significant, negative business impact. It is a major source of risk. |
| Deployment Frequency | Continuous and proactive. It is a clear sign that a team is achieving a high level of performance and balancing the speed of delivery with the stability of the system. | Infrequent and scheduled. A team conducts tests on an infrequent basis, a major source of risk. |
| Testing Frequency | Continuous and proactive. It is a clear sign that a team is achieving a high level of performance and balancing the speed of delivery with the stability of the system. | Infrequent and scheduled. A team conducts tests on an infrequent basis, a major source of risk. |
| Testing Frequency | Continuous and proactive. It is a clear sign that a team is achieving a high level of performance and balancing the speed of delivery with the stability of the system. | Infrequent and scheduled. A team conducts tests on an infrequent basis, a major source of risk. |
| Testing Frequency | Continuous and proactive. It is a clear sign that a team is achieving a high level of performance and balancing the speed of delivery with the stability of the system. | Infrequent and scheduled. A team conducts tests on an infrequent basis, a major source of risk. |
Tools and Technologies That Power Automation
The business value of a proactive IaC strategy is not just about reducing the risk of a new feature; it is also about providing a new, modern, and high-quality product to a user. It is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
- Increased Confidence: A proactive IaC strategy can lead to a high level of confidence in a new version of an application. By providing a clear, transparent, and auditable record of all the components that are used in an application, it allows an organization to embed security and compliance into every stage of the CI/CD pipeline.
- Faster Time to Market: A proactive IaC strategy can lead to a faster time to market. By providing a new, modern, and high-quality product to a user, a team can be more responsive to a user's needs and can provide a new, modern, and high-quality product that is more resilient to a bug or a performance issue.
- Improved Team Morale: A proactive IaC strategy can lead to a high level of team morale. The constant need for a new, modern, and high-quality product can lead to a high level of burnout and a high level of turnover. It is a clear sign that a team is not achieving a high level of performance and that it is not balancing the speed of delivery with the stability of the system.
Security and Compliance Through Automation
The role of a container in a modern software supply chain is a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a declarative, automated, and scalable way to manage a complex, distributed system. The container is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world. It is a strategic investment that pays dividends in terms of speed, quality, and risk reduction. The modern solution to this problem is a robust security strategy. It is a set of strategies that are used to manage a complex, distributed system in a secure, compliant, and auditable way. This proactive approach not only reduces risk but also empowers teams to move faster and to be more confident in their code.
Conclusion
In the end, leveraging a robust IaC strategy is not just a technical artifact; it is a strategic tool that is essential for achieving the security, the compliance, and the business value that are required in a modern DevOps practice. By providing a clear, transparent, and auditable record of all the components that are used in an application, it allows an organization to embed security and compliance into every stage of the CI/CD pipeline. This proactive approach not only reduces risk but also empowers teams to move faster and to be more confident in their code. It is a key part of a modern software supply chain management strategy and is a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world. It is a strategic investment that pays dividends in terms of speed, quality, and risk reduction.
Frequently Asked Questions
What is a CI/CD Pipeline?
A CI/CD pipeline is a major source of risk and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. It is a vulnerability that is unknown to a developer and that is not yet patched. If a zero-day vulnerability is exploited, it can have a significant, negative business impact.
How does a CI/CD Pipeline impact a pipeline?
The impact of a CI/CD pipeline on a pipeline is a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a significant, negative business impact. It can lead to a data breach, a loss of a customer's trust, and a compromised environment.
How do we handle a CI/CD Pipeline?
The modern solution to the challenges of managing a CI/CD pipeline strategy is a robust security strategy. It is a set of strategies that are used to detect, to respond to, and to mitigate a zero-day vulnerability in a secure, compliant, and auditable way. It is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
What is a proactive scanning?
A proactive scanning is a set of strategies that are used to detect a zero-day vulnerability in a proactive way. This can be done with a set of tools that can provide a clear, objective, and data-driven way to measure the performance of a new version of an application. It is a key part of a modern DevOps practice.
What is an incident response plan?
An incident response plan is a set of strategies that are used to respond to a zero-day vulnerability in a timely and in a secure way. This can be done with a set of tools that can provide a clear, objective, and data-driven way to measure the performance of a new version of an application. It is a key part of a modern DevOps practice.
What is the role of a container in a modern software supply chain?
The role of a container in a modern software supply chain is a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a declarative, automated, and scalable way to manage a complex, distributed system. It is a key part of a modern DevOps practice.
What is a software supply chain?
A software supply chain is a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a declarative, automated, and scalable way to manage a complex, distributed system. It is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
How does a container help with scalability?
A container is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world. It is a strategic investment that pays dividends in terms of speed, quality, and risk reduction. It is a key part of a modern software supply chain management strategy.
What is the role of CI/CD in security?
The role of CI/CD in a security strategy is to automate the process of building, testing, and deploying an application. This is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world. It is a key part of a modern business strategy and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
What is the business value of a proactive security strategy?
The business value of a proactive security strategy is a high level of confidence in a new version of an application, a faster time to market, and an improved team morale. It is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
How does a security strategy ensure compliance?
A robust security strategy ensures compliance by providing a clear, transparent, and auditable record of all the components that are used in an application. This allows an organization to embed security and compliance into every stage of the CI/CD pipeline. This proactive approach not only reduces risk but also empowers teams to move faster and to be more confident in their code.
Is it possible to use a security strategy with legacy systems?
It is possible to use a security strategy with legacy systems, but it can be a significant challenge. A legacy system often has a significant amount of state and was not designed for a modern, automated, and continuous delivery process. It is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
How does a security strategy improve a security posture?
A robust security strategy improves a security posture by providing a clear, transparent, and auditable record of all the components that are used in an application. This allows an organization to embed security and compliance into every stage of the CI/CD pipeline. This proactive approach not only reduces risk but also empowers teams to move faster and to be more confident in their code.
How does a security strategy help with audits?
A robust security strategy helps with audits by providing a clear, transparent, and auditable record of all the components that are used in an application. This allows an organization to embed security and compliance into every stage of the CI/CD pipeline. This proactive approach not only reduces risk but also empowers teams to move faster and to be more confident in their code.
What are the risks of a poor security strategy?
The risks of a poor security strategy are a significant, negative business impact, a major source of risk, and a clear sign of a lack of a clear, objective, and data-driven way to improve the performance of a team. This can lead to a significant, negative business impact. It is a clear sign that a team is not achieving a high level of performance and that it is not balancing the speed of delivery with the stability of the system.
What is a CVE?
A Common Vulnerabilities and Exposures (CVE) is a list of publicly disclosed cybersecurity vulnerabilities. It is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world. It is a strategic investment that pays dividends in terms of speed, quality, and risk reduction.
What is the difference between a zero-day and a known vulnerability?
The difference between a zero-day and a known vulnerability is that a zero-day is a vulnerability that is unknown to a developer and that is not yet patched. A known vulnerability is a vulnerability that is known to a developer and that has a patch. It is a clear sign that a team is not achieving a high level of performance and that it is not balancing the speed of delivery with the stability of the system.
What is a container?
A container is a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a new, modern, and high-quality product to a user: a declarative, automated, and scalable way to manage a complex, distributed system. It is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
What is the role of continuous delivery in security?
The role of continuous delivery in a security strategy is to automate the process of deploying an application. This is a key part of a modern DevOps practice and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world. It is a key part of a modern business strategy and a prerequisite for achieving the speed, reliability, and security that are required in today's cloud-native world.
What is the difference between a security and a vulnerability scanner?
A security scanner is a set of strategies that are used to detect a zero-day vulnerability in a proactive way. A vulnerability scanner is a set of strategies that are used to detect a vulnerability in a proactive way. It is a clear sign that a team is not achieving a high level of performance and that it is not balancing the speed of delivery with the stability of the system.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0
































![Kong Interview Preparation Guide [2025]](https://www.devopstraininginstitute.com/blog/uploads/images/202509/image_430x256_68dbb95326997.jpg)




















![100+ Azure DevOps Interview Questions and Answers [Updated 2025]](https://www.devopstraininginstitute.com/blog/uploads/images/202509/image_140x98_68c40aa9a3834.jpg)






![Future Scope of DevOps Careers in Pune [Updated 2025]](https://www.devopstraininginstitute.com/blog/uploads/images/202510/image_140x98_68e3a84652312.jpg)


